Zero-Day Exploits: What They Are, Why They’re Surging in 2026 & How Enterprise Organizations Respond
Zero-day exploits are exploding in enterprise environments because organizations are expanding their digital footprint faster than they can secure it. The rapid adoption of cloud platforms, APIs, remote work infrastructure, and AI-driven tools has created a vastly larger attack surface, often with hidden or poorly understood vulnerabilities.
At the same time, sophisticated threat actors—including nation-states and organized cybercrime groups—are investing heavily in discovering and weaponizing previously unknown flaws before vendors can patch them.
Zero-Day Exploits: What They Are, Why They’re Crushing Enterprise Organizations, and How This Actually Hits You
Zero-day exploits are one of those cybersecurity topics people nod at… until one lands in their environment. Then it’s all-hands-on-deck, change freezes get broken, and leadership wants answers yesterday.
A zero-day exploit is when attackers take advantage of a software or hardware vulnerability before the vendor knows about it or before a patch exists. No warning. No fix. No grace period. The attackers are already inside while defenders are still figuring out what happened.
And right now, zero-days are hitting enterprise organizations harder than ever—not because enterprises are careless, but because of how modern enterprise tech actually works.
Why Zero-Day Exploits Are Exploding in Enterprise Environments
Here’s the uncomfortable truth: enterprises are prime targets because one successful exploit can unlock an entire ecosystem.
Attackers aren’t just hunting desktops anymore. They’re aiming straight at:
- Email security platforms
- VPNs and remote access tools
- Identity providers (SSO, IAM, MFA systems)
- Firewalls, WAFs, and network appliances
- Cloud management and admin consoles
Why? Because compromising one of these systems gives attackers leverage, scale, and persistence. In plain language: if attackers can break the thing you trust to protect everything else, the game changes fast.
What Actually Happens When a Zero-Day Hits an Enterprise
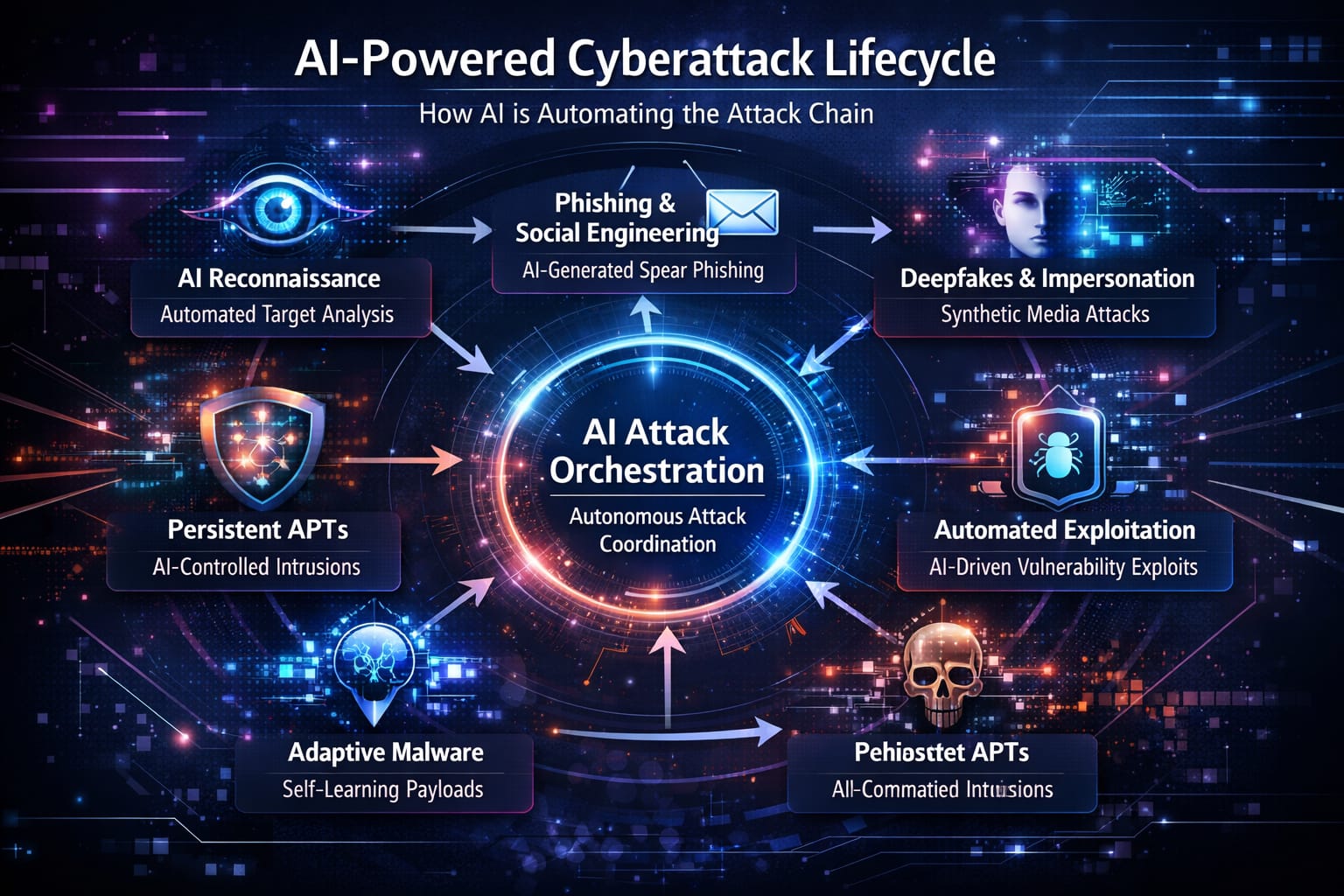
Zero-days don’t usually start with chaos. They start quietly.
Step 1: Initial foothold
An attacker exploits the vulnerability to gain access—often remote code execution or authentication bypass. This is usually against an internet-facing system that can’t be hidden or shut off easily.
Step 2: Persistence
The attacker drops backdoors, creates hidden admin accounts, installs scheduled tasks, or modifies configs so they can come back even after reboots or partial fixes.
Step 3: Credential harvesting
Once inside, they go hunting for:
- Admin credentials
- API keys
- Tokens
- Service accounts
- SSO trust relationships
At this point, the original zero-day almost doesn’t matter anymore.
Step 4: Lateral movement
They pivot across the environment—cloud, on-prem, SaaS—using legitimate credentials. This is where detection usually fails, because activity looks “normal.”
Step 5: Monetization
This shows up as:
- Ransomware
- Data theft and extortion
- Espionage
- Business disruption
By the time leadership hears about it, the attackers may have been inside for weeks.
Why Zero-Days Are Worse Than “Regular” Vulnerabilities
Most security programs are built around known risks: CVEs with patches, regular patch cycles, vulnerability scanners, and scheduled maintenance windows. Zero-days blow that model up.
No patch on day one
You can’t patch what doesn’t exist yet. That means your normal controls are already behind.
Detection is delayed
Security tools rely heavily on signatures, patterns, and known behaviors. Zero-days don’t match those—at first.
Change control breaks down
Emergency patching and mitigation often means production changes without full testing, partial mitigations, and risky config changes under pressure. That’s how outages and secondary incidents happen.
Why Enterprise Tech Is the New Favorite Target
There’s been a noticeable shift away from “spray and pray” endpoint attacks toward enterprise infrastructure attacks.
From an attacker’s perspective:
- One firewall bug > 10,000 phishing emails
- One SSO exploit > hundreds of stolen passwords
- One email gateway exploit > full internal visibility
Security tools, ironically, are now some of the most valuable targets because they sit in privileged positions with broad access.
The Real Business Impact (Not Just Security Pain)
Zero-days don’t just hurt security teams. They hit the business where it hurts most.
Operational disruption
- Email down
- VPN access broken
- Cloud admin access restricted
- E-commerce or internal systems offline
Revenue doesn’t wait for incident response to finish.
Financial damage
- Incident response firms
- Forensics
- Legal counsel
- Emergency consulting
- Tool replacements
- Overtime and burnout
Even without ransomware, the bill adds up fast.
Regulatory and compliance fallout
Depending on your industry, you may face breach notification requirements, audits, fines, contractual penalties, and customer reporting obligations. Zero-day incidents often trigger extra scrutiny because of their scale and sensitivity.
Trust erosion
Customers and partners don’t care that it was a “zero-day.” They care that data was exposed, systems were unavailable, and security controls failed. Reputation damage lasts longer than the outage.
Why “Just Patch It” Is Not Enough
A common mistake enterprises make is thinking the problem ends once a patch is applied. It doesn’t.
If attackers exploited the vulnerability before the patch, they may already have new admin accounts, stolen credentials, persistence mechanisms, or hidden tunnels or services.
That’s why zero-day response has to assume potential compromise, not just vulnerability exposure.
What Smart Enterprises Do Differently
Enterprises that handle zero-days well don’t panic—but they move fast and deliberately.
1) Prioritize based on real exploitation
Not every scary vulnerability matters equally. Smart teams focus on actively exploited vulnerabilities, internet-facing systems, and identity/email/edge infrastructure. This keeps teams from burning out on noise.
2) Treat edge systems as crown jewels
Minimum baseline should include:
- No public management interfaces
- Strong MFA for all admin access
- Separate admin accounts
- Regular review of configs and access logs
If attackers own the edge, they own the map.
3) Hunt, don’t just patch
After mitigation:
- Review logs before and after the patch window
- Look for new admin users, tokens, or keys
- Check for persistence mechanisms
- Rotate credentials where exposure is possible
Assume attackers tried to stay.
4) Reduce blast radius
You won’t prevent every zero-day. You can limit the damage with:
- Network segmentation
- Least-privilege access
- Separate identity tiers
- Protected backups and recovery paths
Slowing attackers down buys detection time.
5) Build an emergency response lane
Zero-days ignore calendars. You need:
- Pre-approved emergency change processes
- Clear system ownership
- Fast communication paths
- Leadership alignment before the crisis
If you wait to define this during an incident, you’re already behind.
What Leadership Needs to Understand (Without the Jargon)
If you had to explain zero-day risk in one breath:
“Zero-days bypass normal defenses, target the systems we trust most, and can compromise large parts of the business before we even know there’s a problem. Our goal isn’t perfection—it’s fast detection, limited blast radius, and controlled recovery.”
That framing changes conversations from blame to readiness.
The Bottom Line
Zero-day exploits are not rare edge cases anymore. They’re a core enterprise risk, especially as attackers focus on infrastructure, identity, and security platforms.
You can’t prevent every zero-day. But you can detect faster, respond smarter, contain damage, and recover cleanly.
Enterprises that accept that reality—and build for it—are the ones that survive the next zero-day without it becoming a headline.