The Death of the Traditional SOC: Why Legacy Security Operations Are Being Replaced by AI-Driven Models
The Death of the Traditional SOC
Why legacy security operations can’t keep up with AI-driven threats, cloud sprawl, and identity-centric attacks — and what replaces the old SOC model.
Cybersecurity • SOC Modernization • AI & Automation
For nearly two decades, the Security Operations Center (SOC) has been the backbone of enterprise cybersecurity. Rows of analysts monitoring dashboards, triaging alerts, and manually responding to threats once represented the gold standard of digital defense.
But today, that model is breaking down. Modern enterprises now operate in cloud-first, AI-powered, identity-driven environments that change by the minute. Attackers move faster than ever, powered by automation, ransomware-as-a-service, and AI-driven phishing. Meanwhile, traditional SOCs remain trapped in outdated architectures, overwhelmed by alerts, and starved for skilled talent.
The result is unavoidable: the traditional SOC is dying. Not because security no longer matters, but because the old way of doing security operations no longer works.
What the Traditional SOC Was Built For
The traditional SOC was designed for a very different era of computing. Its foundations were built around:
- On-premise data centers and static infrastructure
- Perimeter-based security and network-centric monitoring
- Log-focused SIEM platforms as the primary data hub
- Tiered analysts manually triaging and escalating alerts
This model assumed that most assets lived inside a controlled network and that threats followed predictable patterns. For many years, it worked well enough. But that world is gone.
Why the Traditional SOC Is Failing Today
The cracks in the traditional SOC are now impossible to ignore. Between alert overload, tool sprawl, cloud complexity, and a brutal talent shortage, legacy approaches simply can’t keep up with the speed and sophistication of modern attacks.
1. Alert Overload Has Destroyed Effectiveness
Modern environments generate an astronomical volume of security telemetry from endpoints, cloud workloads, SaaS platforms, APIs, identities, and IoT devices. Every security tool produces alerts, and most of them are low quality.
Analysts now spend most of their time closing false positives instead of stopping real attacks. This leads to:
- Slower detection and response times
- Missed critical incidents hidden in the noise
- Analyst burnout and high turnover
When too many alerts are treated as emergencies, none of them truly are.
2. Tool Sprawl Has Fragmented Visibility
Instead of one cohesive security platform, most organizations now run a patchwork of SIEM, EDR, NDR, cloud security, email security, identity tools, and more. Each system sees only a slice of reality, and none see the full attack chain end to end.
Correlating activity across these tools requires manual effort, brittle integrations, and complex playbooks. This fractured visibility gives attackers exactly what they want: blind spots and time to move laterally.
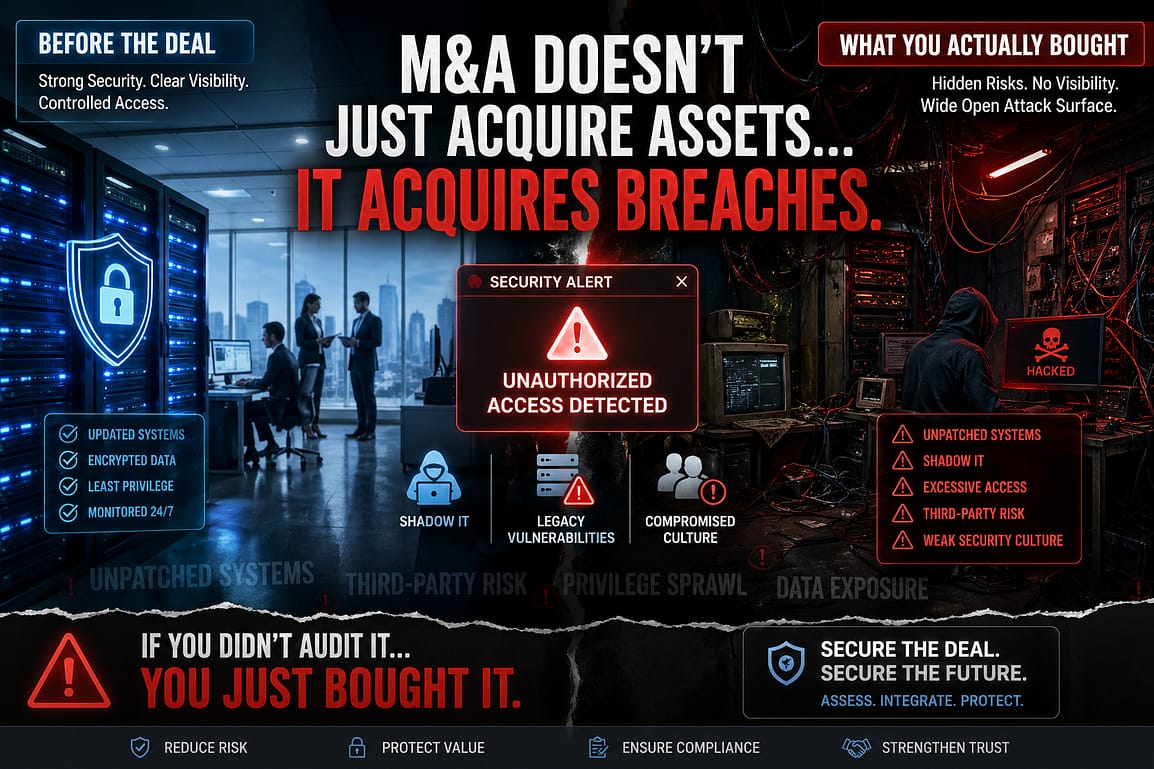
3. Legacy Architecture Can’t Protect Cloud & Identity
Traditional SOCs were designed around networks and perimeters. Modern attacks are designed around credentials, tokens, APIs, and misconfigurations.
Today’s breaches often begin with compromised identities, OAuth abuse, MFA fatigue attacks, API key leaks, or cloud misconfigurations. Legacy SOC tooling wasn’t built to understand cloud-native behavior or identity-driven attack paths at scale.
4. The Talent Crisis Has Broken the SOC Model
To run a true 24/7 SOC, organizations need tiered analysts, threat hunters, detection engineers, cloud security experts, and incident responders. Very few companies can staff all these roles internally, and even fewer can retain them long term.
As salaries rise and burnout increases, it’s clear that security operations can no longer depend on human-only scaling.
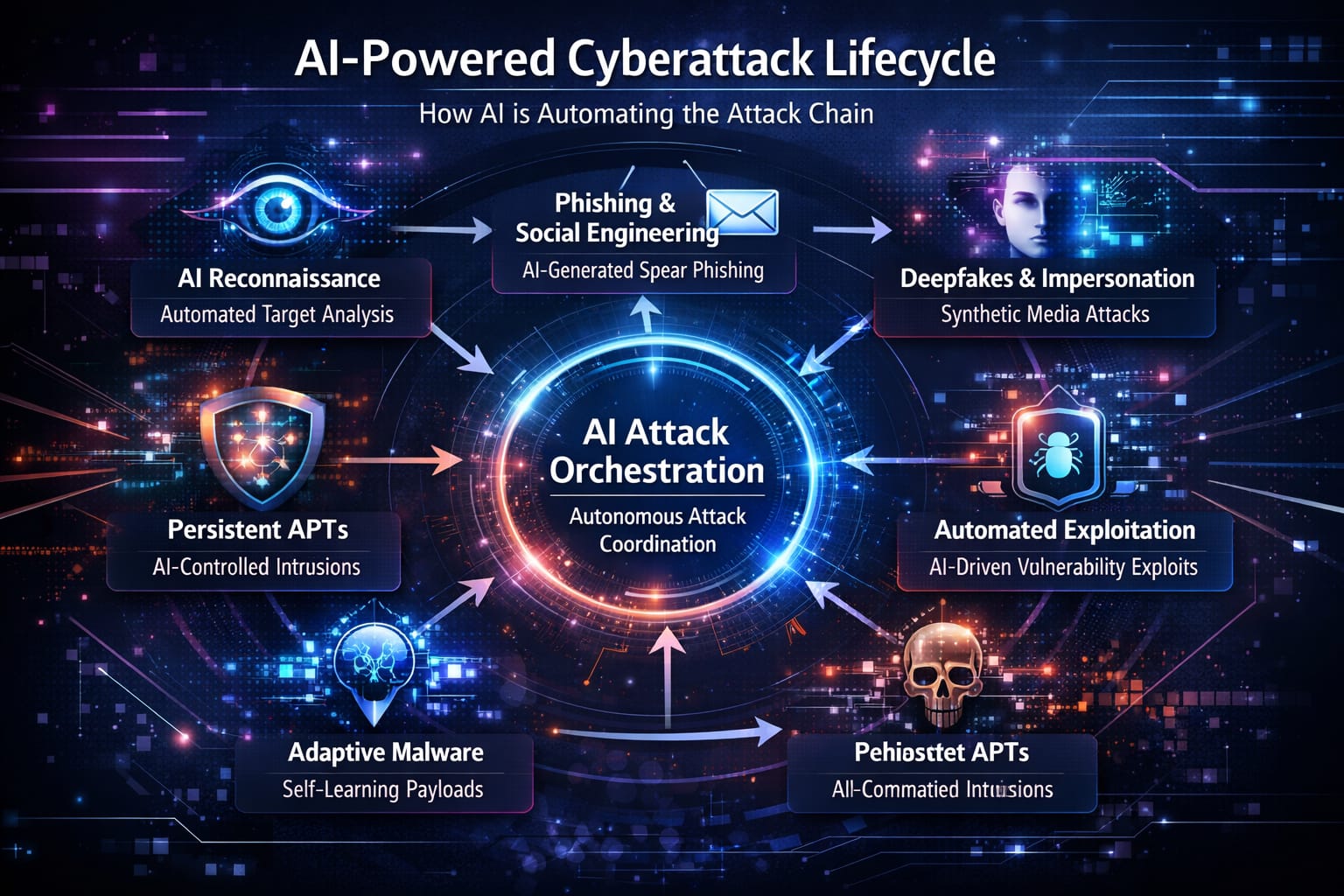
5. Attackers Now Move at Machine Speed
Threat actors leverage AI-generated phishing, automated exploit kits, and rapidly shifting infrastructure that spins up and disappears in minutes. Meanwhile, traditional SOC processes still depend on ticket queues, manual escalations, and human-only investigations.
This time gap is fatal. The old SOC model simply can’t react as quickly as adversaries can innovate.
The Rise of the New SOC Model
The death of the traditional SOC doesn’t mean the end of security operations. It marks the beginning of a new operating model — one that is AI-driven, platform-based, automation-first, and far more closely aligned with how modern businesses run.
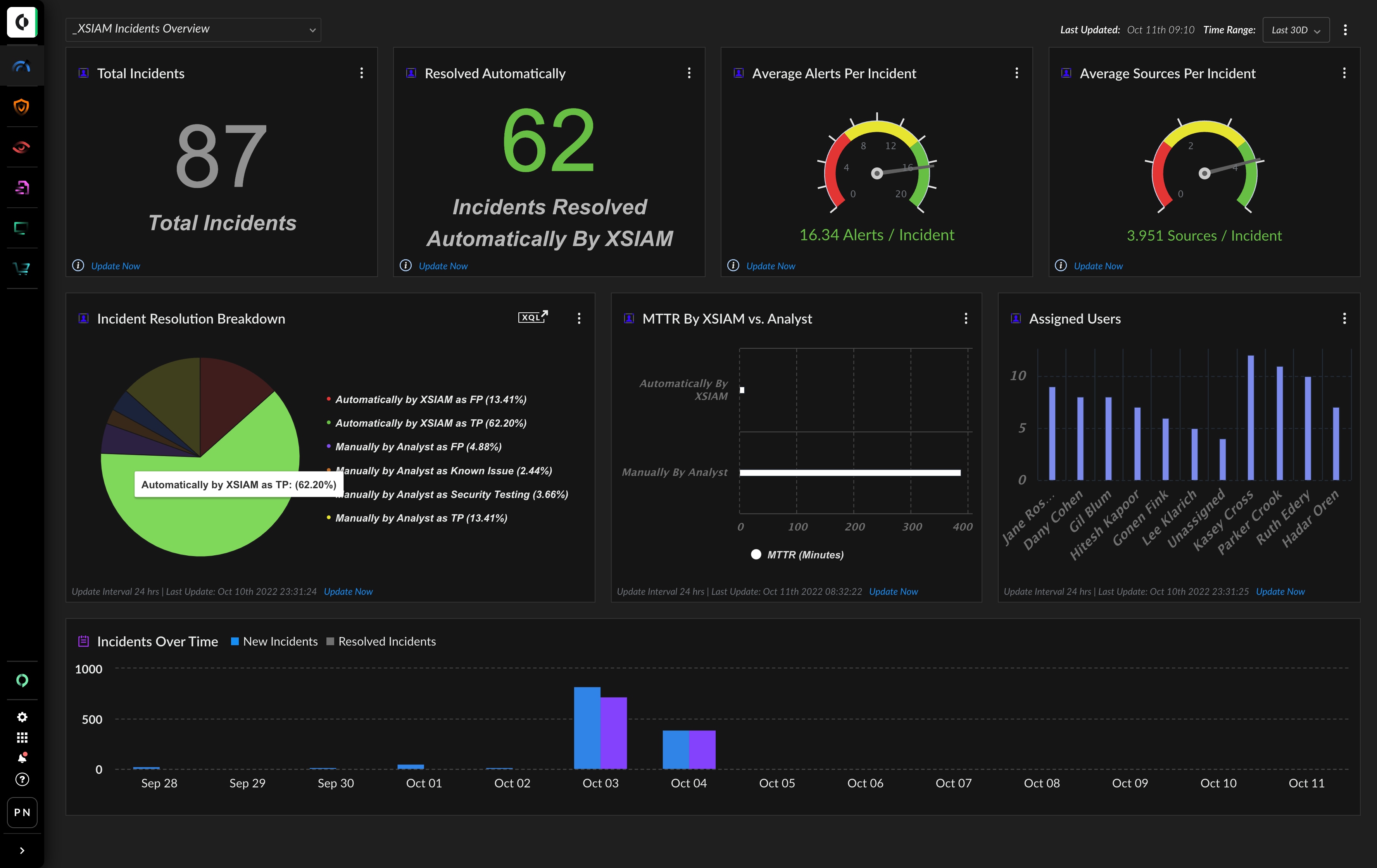
1. AI-Powered Detection & Response
Modern SOC platforms use artificial intelligence to analyze millions of events in real time, automatically suppress false positives, correlate threats across tools, and prioritize the small set of incidents that truly matter.
AI now handles the volume. Humans handle the judgment. This shift eliminates the single biggest pain point of the traditional SOC: endless alert floods.
2. XDR Is Replacing the SIEM-Centric SOC
Extended Detection and Response (XDR) unifies endpoint, network, email, cloud, and identity telemetry into one detection and response engine. Instead of bolt-on tools stitched together with custom integrations, XDR becomes a single security brain for the organization.
The SOC no longer revolves around raw logs. It revolves around high-fidelity, behavior-based detection.
3. MDR Has Become the New SOC for Many Organizations
Managed Detection and Response (MDR) delivers SOC capability as a service. Instead of building a 24/7 internal team, organizations partner with experts who provide continuous monitoring, investigation, and guided response.
MDR instantly addresses talent gaps, night-shift coverage, and alert fatigue, making enterprise-grade detection and response accessible to mid-market and resource-constrained teams.
4. Autonomous SOCs Are Already Emerging
The next phase of security operations is the autonomous or agentic SOC. AI agents can investigate suspicious activity, enrich alerts, map attack paths, and recommend or execute containment actions within defined guardrails.
Instead of analysts reacting to queues, AI agents continuously hunt across the environment. Humans supervise strategy and tune automation rather than manually clicking through every alert.
Humans Aren’t Being Replaced — Their Role Is Being Upgraded
The death of the traditional SOC does not mean the end of security analysts. It means the end of low-level manual security labor.
In the new SOC model, human experts focus on:
- Threat hunting and adversary emulation
- Detection engineering and content tuning
- Automation and playbook design
- Red and purple team collaboration
- Security architecture and resilience strategy
- Incident command during major events
Security operations becomes a high-skill engineering discipline — not a reactive call center.
How to Transition Away from the Traditional SOC
The shift doesn’t happen overnight, but it has to be intentional. Organizations that modernize their SOC gain faster detection, smarter response, and better alignment with business risk.
Practical Steps to Modernize
- Audit your alert reality — measure alert volume, false positive rate, and time-to-respond.
- Consolidate detection platforms — move toward unified XDR instead of fragmented point tools.
- Automate Tier 1 and Tier 2 tasks — let machines handle repetitive triage and enrichment.
- Leverage MDR strategically — use SOC-as-a-service to cover 24/7 monitoring and first-line response.
- Redefine analyst roles — upskill your team into hunters, engineers, and automation owners.
- Tie SOC success to business outcomes — focus on breach prevention, downtime avoided, and risk reduction, not ticket counts.
The SOC Isn’t Dead — Only the Old One Is
The traditional SOC — manual, SIEM-heavy, alert-driven, and analyst-dependent — cannot survive in a cloud-first, AI-powered threat landscape. But security operations themselves are more important than ever.
The future belongs to AI-driven detection, autonomous response, MDR-enabled operations, and unified XDR platforms backed by human-led strategy and machine-scale execution.
The traditional SOC is dead. The autonomous SOC has arrived.
Talk to Us About Modernizing Your SOC