Cloud Misconfiguration Crisis: How Simple Setup Mistakes Expose Enterprise Data at Scale
Most organizations believe their cloud is secure. They trust the provider. They trust their tools. They trust the architecture diagrams that show locks, shields, and encrypted tunnels. And yet, sensitive data quietly slips into the open internet through nothing more than a simple configuration mistake.
This is the real cloud security crisis. It is not driven by elite hackers or cutting-edge exploits. It is driven by everyday human error. A checkbox left enabled. A permission granted too broadly. A test environment promoted into production without proper safeguards. These small oversights are responsible for many real-world cloud breaches today.
The uncomfortable truth is this: your cloud is probably more exposed than you think.
What Cloud Misconfiguration Really Means
Cloud misconfiguration simply means that a cloud service has been set up in an unsafe way. It might be a storage bucket that should be private but is publicly accessible. It might be a firewall rule that allows traffic from anywhere. It might be an identity account with far more permissions than it actually needs. None of these look dangerous on their own. Together, they create a wide-open attack surface.
Cloud misconfigurations do not usually happen out of carelessness. They happen because cloud environments move fast. Developers are under pressure to deploy quickly. Teams copy templates from previous projects. Test environments become permanent. Temporary access becomes permanent access. Over time, small risks quietly stack on top of each other.
Eventually, someone finds them.
Why Attackers Love Misconfigured Clouds
Attackers do not need advanced tools to abuse misconfigured cloud environments. They use automated scanners that constantly search the internet for exposed cloud resources. When something is accidentally made public, it is often found quickly.
Once something is found, the damage does not always look dramatic at first. Data may be quietly downloaded without triggering alarms. Credentials might be harvested and used later. Entire environments may be mapped silently before a single disruptive move is made.
Many organizations only realize they have been compromised when customers report leaked data, regulators request responses, or news outlets call for comment. By then, the damage is already done.
The Illusion of Shared Responsibility
One of the biggest drivers of cloud misconfigurations is misunderstanding who is responsible for what. Cloud providers secure the physical infrastructure. They protect the data centers, hardware, and underlying platform. What they do not secure is how your organization configures services, manages identity, controls access, and classifies data.
This misunderstanding creates a false sense of safety. Leadership assumes the cloud provider is handling security. Engineering teams assume security tools will catch any mistakes. Security teams assume configurations are locked down by default. In reality, no one is fully accountable for the last mile of cloud security.
That last mile is where most breaches happen.
Why Even Mature Organizations Struggle
Misconfiguration is not just a startup problem. Large enterprises struggle just as much, often more. Their environments are larger, more complex, and spread across multiple clouds, regions, and providers. They run hybrid systems with on-prem and cloud workloads interconnected. They rely on many identities, service accounts, APIs, and automation workflows.
Every one of those components is a potential misconfiguration point.
Change makes the problem worse. New features are launched continuously. Acquisition brings in unfamiliar environments. Engineers move between teams. Documentation falls behind reality. Security ownership becomes fragmented.
The result is an environment where no single person really understands the full risk picture anymore.
The Business Impact Is Bigger Than Data Loss
When cloud misconfigurations lead to exposure, the damage extends far beyond leaked files. The real cost shows up across the business.
Trust is damaged. Customers question whether your company is safe to do business with. Deals slow down as security reviews become more aggressive. Legal teams get involved. Regulators take notice. Executives are pulled into crisis management. Engineering teams stop building products and shift into emergency remediation mode.
Even after technical issues are fixed, the damage to reputation and momentum can linger for a long time.
Why Scans and Audits Are No Longer Enough
Traditional security strategies rely heavily on periodic audits and occasional vulnerability scans. This approach made sense when infrastructure changed slowly. It does not work in the cloud.
Cloud environments change constantly. New resources are spun up automatically. Configuration drift happens daily. Third-party tools integrate and expand access. Temporary fixes become permanent architecture.
By the time an audit discovers a problem, it may have existed for a long time.
Security in the cloud must be continuous. Anything less is reactive and incomplete.
How Organizations Actually Reduce Misconfiguration Risk
The organizations that successfully control cloud misconfiguration risk tend to share the same mindset. They assume misconfigurations will happen. Their strategy focuses on rapid detection, automatic prevention, and continuous correction.
They build secure defaults directly into infrastructure code so new environments start from a safe baseline. They apply policy enforcement during deployment so unsafe changes never reach production. They continuously monitor their cloud footprint for drift and dangerous exposure. They treat identity and access management as a core security foundation, not a convenience feature.
Most importantly, they integrate security directly into engineering workflows instead of treating it as a last-minute review.
The Role of Automation and Visibility
Misconfiguration at cloud scale cannot be managed manually. There are simply too many moving parts. Automation becomes essential.
Automated posture tools constantly look for unsafe settings, exposed data, overly permissive access, and risky changes. They provide visibility across cloud providers and alert teams quickly. Some even auto-remediate lower-risk issues before humans ever get involved.
This shifts security away from firefighting and toward continuous control.
Why Identity Is the Quiet Accelerator of Breaches
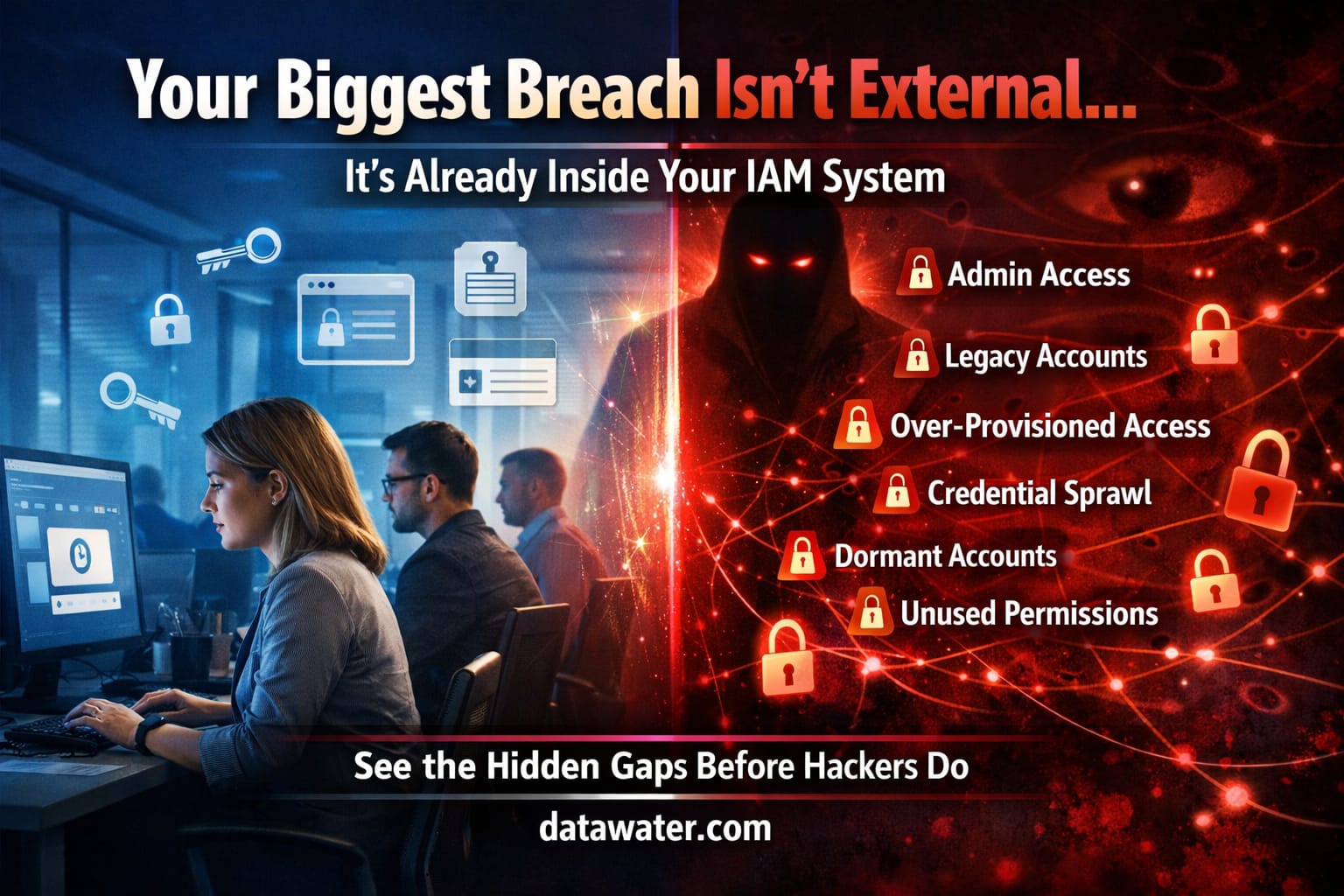
One of the most dangerous misconfiguration patterns is overprivileged identity. When accounts have more access than they need, a single compromised credential can unlock entire environments.
Excess permissions accumulate slowly. Engineers add access for convenience. Temporary access is never revoked. Service accounts gain broad privileges to avoid breaking workloads. Over time, identity becomes the fastest path from a small mistake to a catastrophic breach.
Strong cloud security always starts with strict identity control.
The Cultural Side of the Problem
Technology alone cannot solve misconfiguration. Culture plays just as big a role.
If teams are punished for slowing down deployments, corners will be cut. If security is seen as a blocker instead of an enabler, risk will be hidden rather than discussed. If ownership is unclear, everyone assumes someone else is responsible.
Organizations that succeed in cloud security make secure behavior the easiest behavior. They provide secure templates. They document best practices. They embed security experts alongside engineers. They reward prevention instead of heroics after incidents.
When security becomes part of normal engineering work, misconfigurations drop dramatically.
The New Cloud Security Reality
The era of perimeter-based security is over. In the cloud, there is no clear inside and outside. Everything is exposed to something. Every service is one configuration change away from becoming public.
In this world, the only safe assumption is that misconfigurations will happen. What matters is how fast you detect them, how automatically you correct them, and how deeply security is embedded into your workflows.
The strongest cloud security programs do not rely on hope. They rely on continuous verification.
The Bottom Line
Cloud misconfiguration is no longer a niche technical issue. It is a core business risk. It affects revenue, brand trust, compliance, velocity, and market reputation.
The most dangerous part is not how often misconfigurations happen. It is how quietly they exist before anyone notices.
If your cloud strategy assumes that security is handled by default, then your cloud is already exposed. The only real question is whether you discover the gaps before someone else does.