Post-Merger Integration Security: How M&A Deals Inherit Vulnerable Systems, Shadow IT & Risky Culture
Cybersecurity • M&A Risk • Enterprise Security
Post-Merger Integration Security: How M&A Deals Inherit Insecure Systems, Shadow IT, and Risky Culture
Post-merger integration security is one of the most overlooked threats in mergers and acquisitions. When two companies combine, they do not simply merge revenue, customers, people, and products. They also merge passwords, cloud accounts, vendor contracts, endpoints, unmanaged data, outdated software, privileged users, security habits, and cyber risk.
A deal may look strong on paper, but if the acquiring company inherits insecure systems and a weak security culture, the integration can quickly become a breach waiting to happen.
View PMI Security ChecklistWhy Post-Merger Integration Security Matters
Post-merger integration, often called PMI, is the phase after a merger or acquisition where two organizations begin combining technology, operations, teams, data, and processes. From a cybersecurity perspective, this is one of the most dangerous periods in the entire M&A lifecycle. Attackers know integration creates confusion. Employees are changing roles. Systems are being connected. Identity permissions are being adjusted. Vendors may be granted temporary access. Security teams are under pressure to move quickly. That speed creates opportunity for mistakes.
Cybersecurity should not be treated as a final technical cleanup task after the business integration is complete. It should be built into the deal thesis, due diligence process, Day 1 readiness plan, and long-term operating model. Deloitte has warned that cybersecurity risks in M&A can affect deal value, legal exposure, regulatory obligations, and business reputation. Reuters has also highlighted that cyber due diligence is increasingly nonnegotiable in transactions because hidden weaknesses can create financial and operational damage after close.
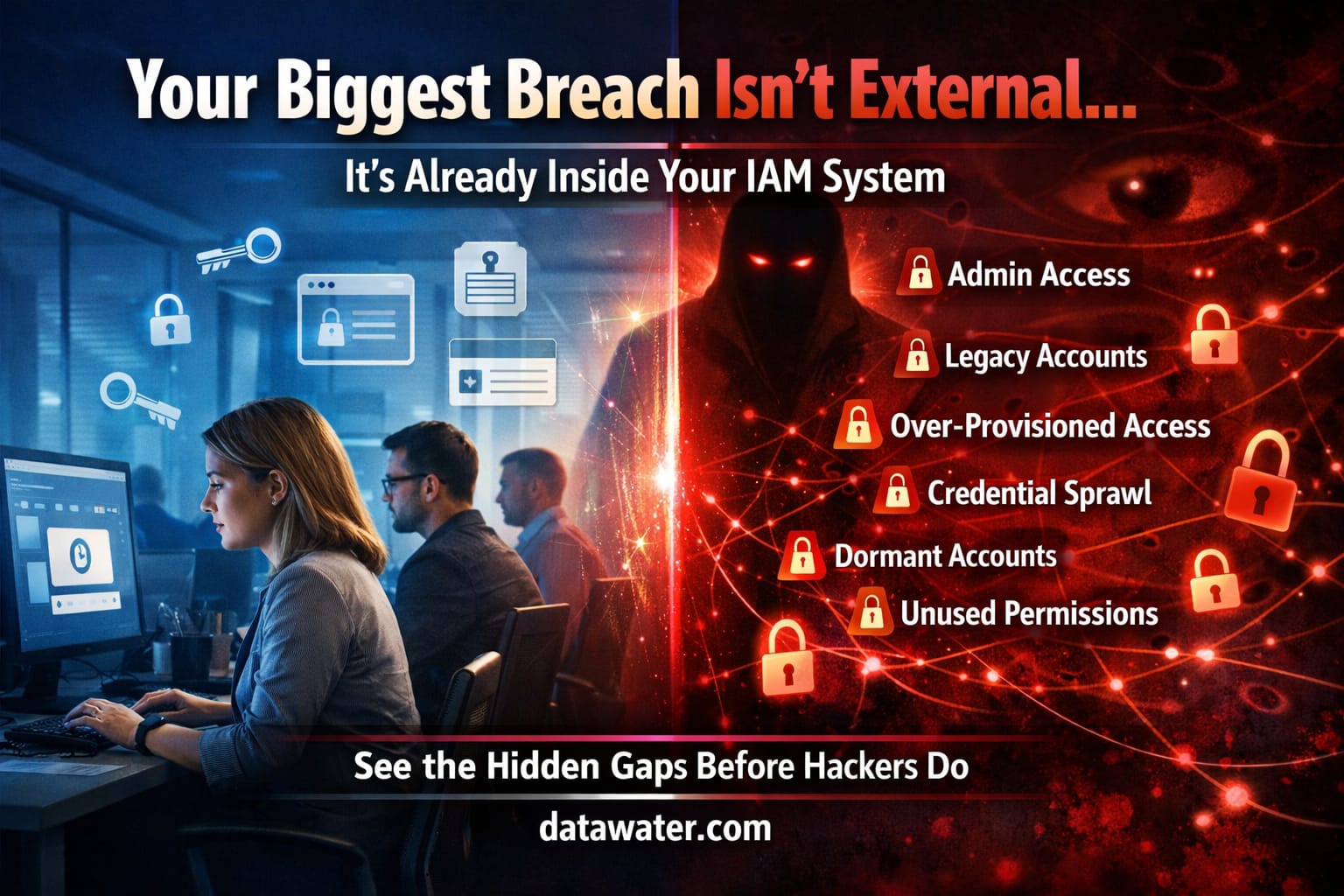
The real problem is simple: the acquiring company often inherits more than assets. It inherits risk. That risk may include compromised accounts, poor endpoint hygiene, unpatched systems, undocumented applications, weak vendor controls, unmanaged cloud storage, old databases, forgotten admin accounts, and a culture where employees were never trained to treat cybersecurity as a business priority.
The Hidden Cyber Risks Companies Inherit During M&A
Many M&A security problems are invisible during early deal conversations. Financial statements may show recurring revenue, strong customer contracts, and growth potential, but the security environment may tell a different story. A target company may have old servers still running critical workloads, employees sharing passwords, SaaS platforms with no single sign-on, weak multifactor authentication, and cloud environments that were built quickly without governance.
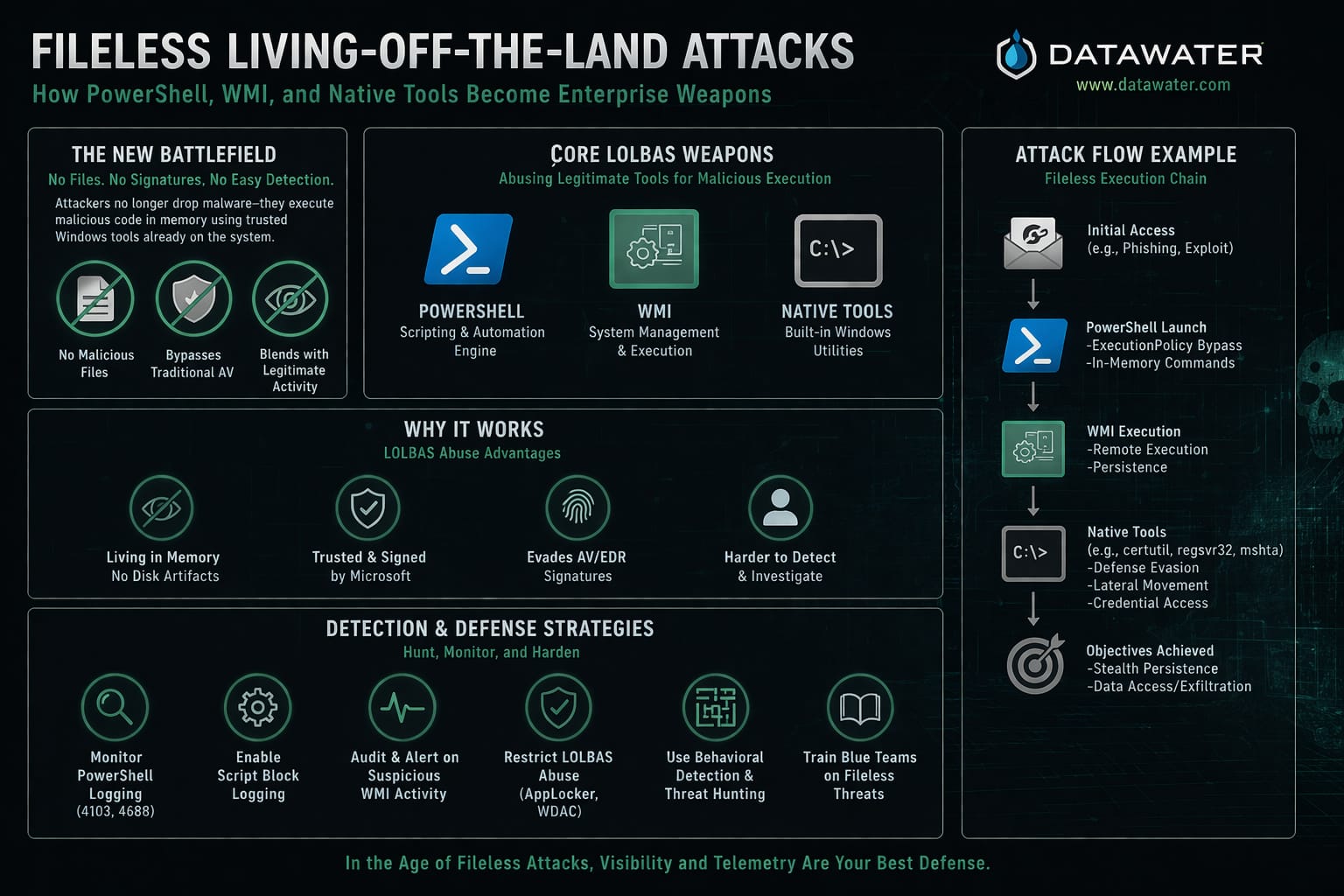
One of the biggest post-merger integration security risks is identity sprawl. When two companies combine, there may be thousands of user accounts across Active Directory, Google Workspace, Microsoft 365, AWS, Azure, GitHub, Salesforce, Slack, HR systems, customer portals, and legacy apps. If nobody knows which accounts are active, which users still need access, and which accounts are privileged, attackers can exploit forgotten credentials.
Another major issue is technical debt. The acquired company may rely on outdated systems because they were “good enough” before the deal. But once connected to the parent company’s network, those old systems become a gateway into a larger, more valuable environment. A small vulnerability inside the acquired company can become a major enterprise breach if integration happens before segmentation, monitoring, and access controls are in place.
Place a cybersecurity-themed image here: two companies merging into one network with red warning signals around legacy servers, cloud apps, and user identities.

Culture Is the Most Dangerous System You Inherit
Post-merger integration security is not only about firewalls, endpoint tools, and access management. Culture is often the deeper issue. If the acquired company has a casual attitude toward security, employees may resist new controls. They may see multifactor authentication, password managers, endpoint agents, phishing training, and access reviews as obstacles instead of protection.
This cultural gap becomes dangerous when the acquiring company assumes everyone follows the same rules. One organization may have mature security operations, formal incident response, clear governance, and executive buy-in. The other may have grown quickly with limited security investment. When these two environments merge, the weaker culture can create friction, mistakes, and shadow workarounds.
Security leaders should treat culture as part of the integration plan. Employees need clear communication about why controls are changing, what risks the company is reducing, and how security protects the value of the merger. The goal is not to punish the acquired company. The goal is to bring both organizations into a stronger operating model.
1. Identity Risk
Review all users, admins, service accounts, contractors, and shared accounts. Remove unnecessary privileges before deep network integration begins.
2. Legacy Systems
Identify unsupported servers, unpatched software, exposed databases, old VPNs, and applications with weak authentication.
3. Security Culture
Train teams early. Align policies, reporting channels, incident response expectations, and executive accountability.
Day 1 Security: What Must Be Ready Before Integration
Day 1 is the moment when the deal becomes operational reality. This is when employees expect access, executives expect momentum, customers expect continuity, and IT teams face pressure to connect systems fast. But fast integration without security guardrails can create major exposure.
Before Day 1, security teams should know which systems are business-critical, which systems are risky, which identities are privileged, which vendors have access, and which data environments contain sensitive information. Network connectivity should be limited and controlled. Access should follow least privilege. Logging should be enabled. Endpoint protection should be deployed or validated. Incident response contacts should be established across both organizations.
Most importantly, the acquiring company should avoid connecting everything at once. A phased integration model is safer. Segment the acquired environment, monitor traffic, validate systems, and gradually connect only what is necessary. This limits the blast radius if hidden malware, compromised credentials, or vulnerable systems are discovered after close.
Post-Merger Integration Security Checklist
- Perform a full asset inventory across endpoints, servers, SaaS, cloud, databases, and network devices.
- Identify all privileged users, service accounts, shared accounts, and dormant accounts.
- Require multifactor authentication for email, VPN, cloud platforms, and administrator access.
- Review endpoint detection, antivirus coverage, patch levels, and device compliance.
- Segment the acquired company’s network before granting broad access to the parent environment.
- Review firewall rules, VPN configurations, open ports, and remote access tools.
- Evaluate data privacy obligations, customer data locations, and regulatory exposure.
- Review third-party vendors, managed service providers, software suppliers, and contractor access.
- Centralize logging into a SIEM or security monitoring platform.
- Run tabletop incident response exercises with both legacy and acquired teams.
- Retire unsupported systems or isolate them until they can be remediated.
- Align security policies, acceptable use standards, phishing reporting, and escalation procedures.
Place a visual checklist image here showing identity, cloud, endpoint, vendor, and culture risks during M&A integration.
Third-Party and Supply Chain Risk After a Merger
Many companies underestimate third-party risk during post-merger integration. The acquired company may have vendors that the parent company has never reviewed. These vendors may have access to sensitive data, production systems, payment information, customer records, code repositories, or operational technology.
NIST defines cybersecurity supply chain risk management as identifying, assessing, and mitigating risks across interconnected ICT and OT supply chains throughout the system lifecycle. In an M&A context, that means the buyer must understand not only the target company’s internal systems, but also the extended ecosystem connected to those systems.
Vendor access should be reviewed immediately. Contracts should be examined for security requirements, breach notification terms, data handling obligations, and audit rights. Vendors with privileged access should be prioritized. Any vendor that cannot meet the acquiring company’s security standards should be remediated, restricted, or replaced.
Security Should Protect the Deal Value
A merger is supposed to create value. Poor post-merger integration security can destroy it. A hidden breach, regulatory violation, ransomware incident, or customer data exposure can turn a strategic acquisition into a reputational crisis.
Build a Secure Integration PlanHow to Build a Strong PMI Security Program
A strong post-merger integration security program should begin before the deal closes. Cybersecurity due diligence should identify high-risk systems, security gaps, regulatory obligations, and integration blockers. The buyer should understand what must be fixed immediately, what can be remediated in phases, and what risks may require financial protection in the purchase agreement.
After close, security teams should operate with a clear roadmap. The first phase should focus on visibility: assets, identities, data, vendors, and vulnerabilities. The second phase should focus on containment: segmentation, access controls, monitoring, and incident response readiness. The third phase should focus on modernization: tool consolidation, cloud governance, endpoint standardization, policy alignment, and security culture development.
Security leaders should also communicate in business language. Executives do not only need a list of vulnerabilities. They need to understand which risks could delay integration, disrupt revenue, create regulatory exposure, or damage customer trust. The best PMI security programs connect technical work to deal value.
Common Mistakes That Make M&A Security Worse
The first mistake is treating security as an IT workstream instead of an executive risk issue. Cybersecurity affects legal, finance, operations, HR, product, customer success, and the board. The second mistake is connecting networks before completing basic discovery. The third mistake is assuming the acquired company’s documentation is complete. Many organizations do not have accurate asset inventories, especially if they grew quickly or acquired smaller companies themselves.
The fourth mistake is ignoring employee behavior. If users are confused, afraid, or frustrated during integration, they may bypass controls. They may keep using old tools, personal devices, unmanaged file-sharing platforms, or legacy communication channels. A strong communication plan reduces this risk.
The fifth mistake is delaying incident response planning. Security teams should assume that unknown issues may surface after close. Having clear escalation paths, legal contacts, forensic support, and executive decision-makers ready can reduce damage if a breach is discovered.
Final Thoughts: M&A Security Is Business Protection
Post-merger integration security is not simply about cleaning up inherited technology. It is about protecting the financial, operational, and strategic value of the deal. Every merger brings complexity. Every acquisition expands the attack surface. Every integration introduces uncertainty. The companies that win are the ones that treat cybersecurity as a core part of integration, not an afterthought.
By focusing on identity, asset discovery, segmentation, vendor risk, monitoring, data governance, and culture, organizations can reduce inherited risk and build a stronger combined enterprise. The goal is not just to merge systems. The goal is to merge securely.
Need a Post-Merger Security Roadmap?
Use this page as a foundation for a security due diligence checklist, executive briefing, integration plan, or cybersecurity landing page for M&A advisory services.
Get a Security Review