-
-
-
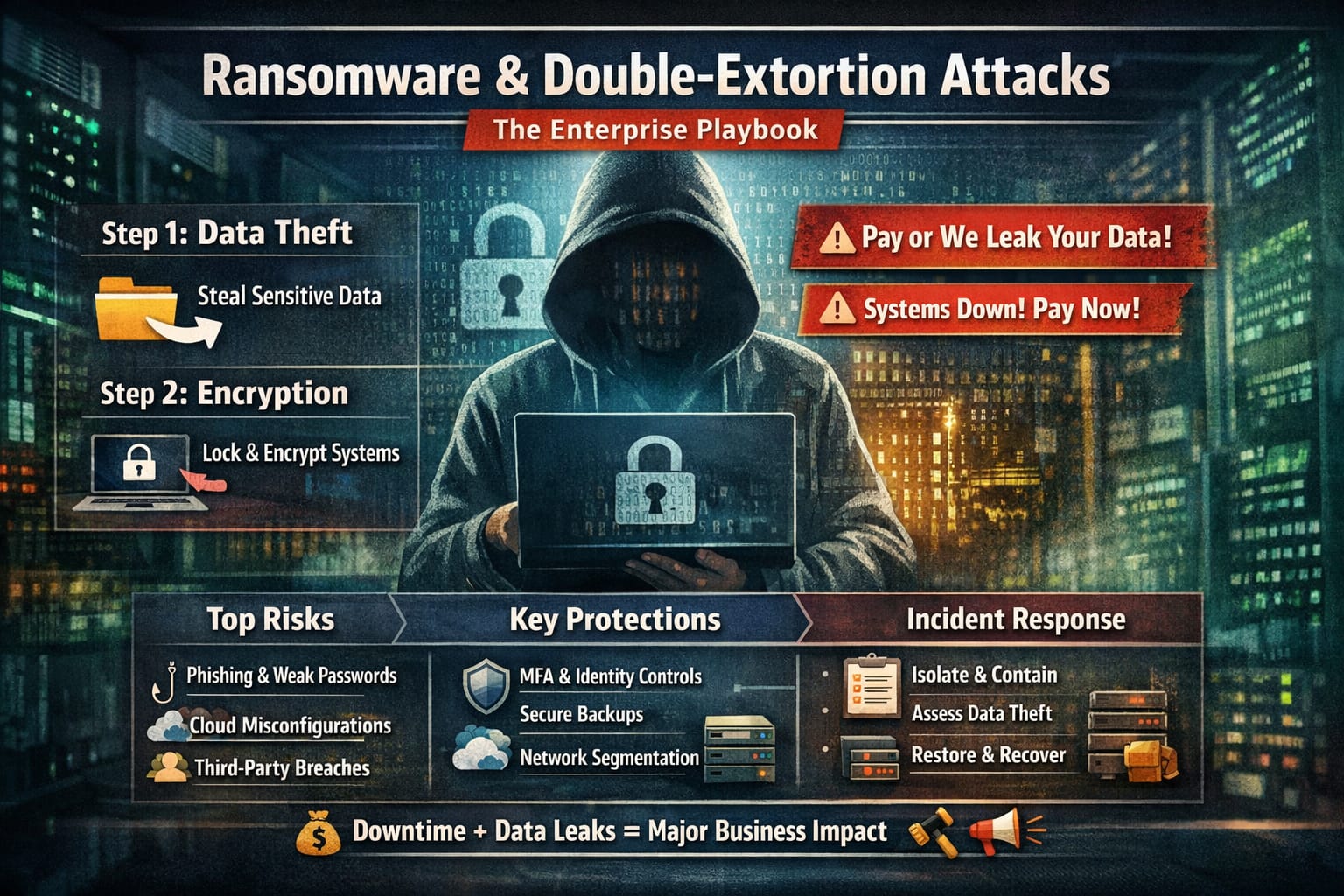
Ransomware & Double-Extortion Attacks: The Enterprise Playbook (Prevention, Detection, Response)
Ransomware & Double-Extortion Attacks: The Enterprise Playbook (Prevention, Detection, Response) Learn how modern ransomware and double-extortion attacks work, why enterprises keep getting hit, and the practical controls that reduce risk—identity hardening, segmentation, backups, detection, and an incident response checklist. Ransomware isn’t just “files get encrypted, pay to unlock.” In today’s enterprise reality, many groups run…
-
API & Application-Layer Attacks: The Enterprise Risk Hiding in Plain Sight
API & Application-Layer Attacks: The Enterprise Risk Hiding in Plain Sight APIs run the modern enterprise. Your mobile app is basically a shell calling APIs. Your customer portal calls APIs. Your partners connect through APIs. Your internal microservices talk to each other through APIs. Even your automation and AI workflows lean on APIs. That’s why…
-
-
-
-
-
-